Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
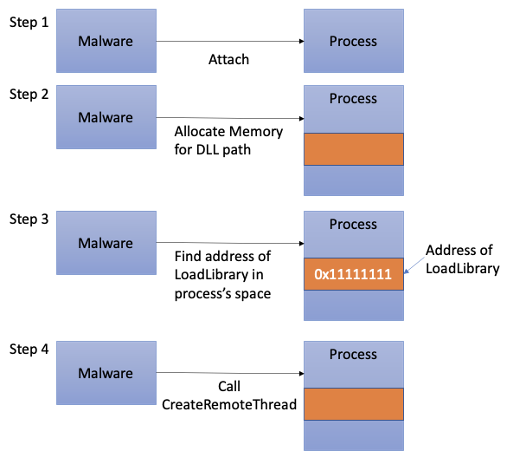
Process Injection Techniques used by Malware, by Angelystor
Linux Commands & Utilities Commonly Used by Attackers

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

How Malicious Actors Abuse Native Linux Tools in Their Attacks

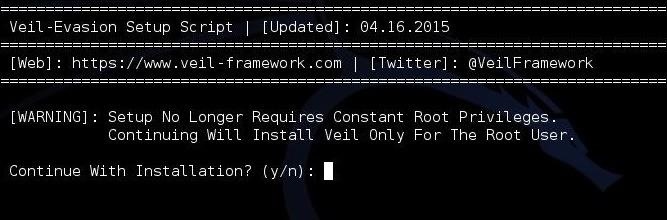
2021-07-01 - Evasive Techniques Used by Malicious Linux Shell

Linux Commands & Utilities Commonly Used by Attackers
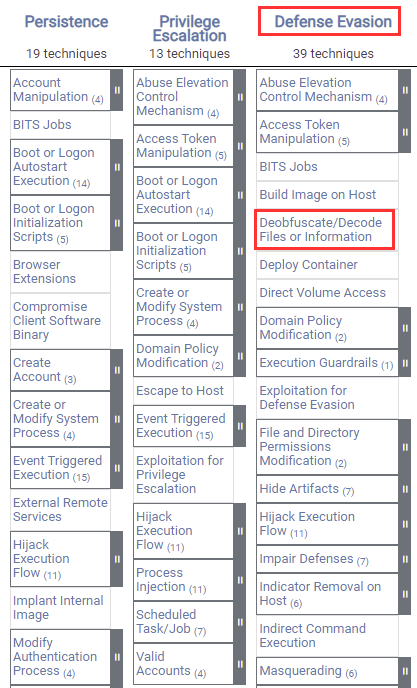
Windows Defense Evasion Techniques
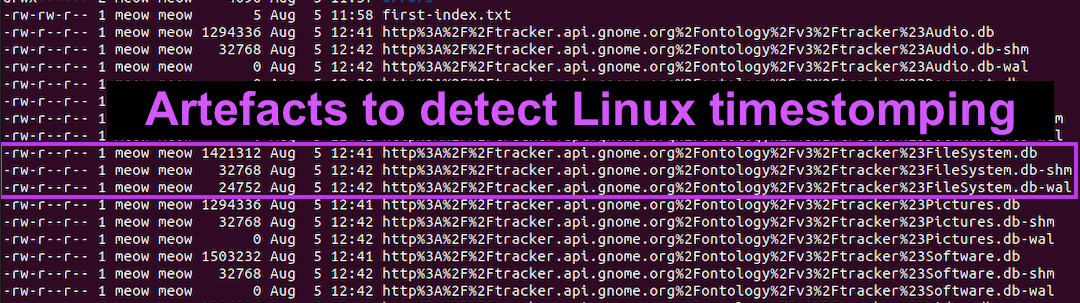
Detecting Linux Anti-Forensics: Timestomping

Six Malicious Linux Shell Scripts Used to Evade Defenses and How