Tactics, Techniques and Procedures (TTPs) Utilized by FireEye's Red Team Tools
Por um escritor misterioso
Descrição
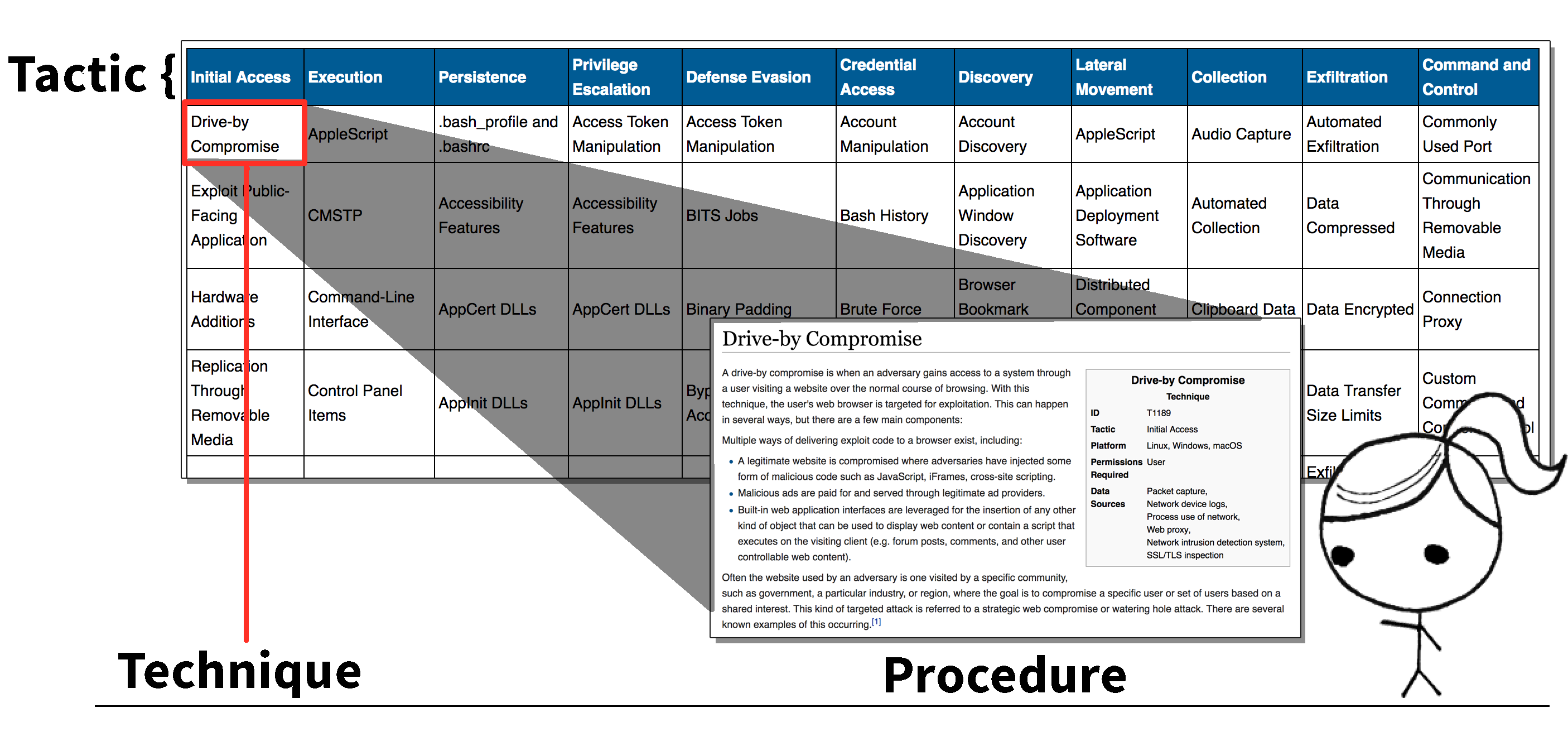
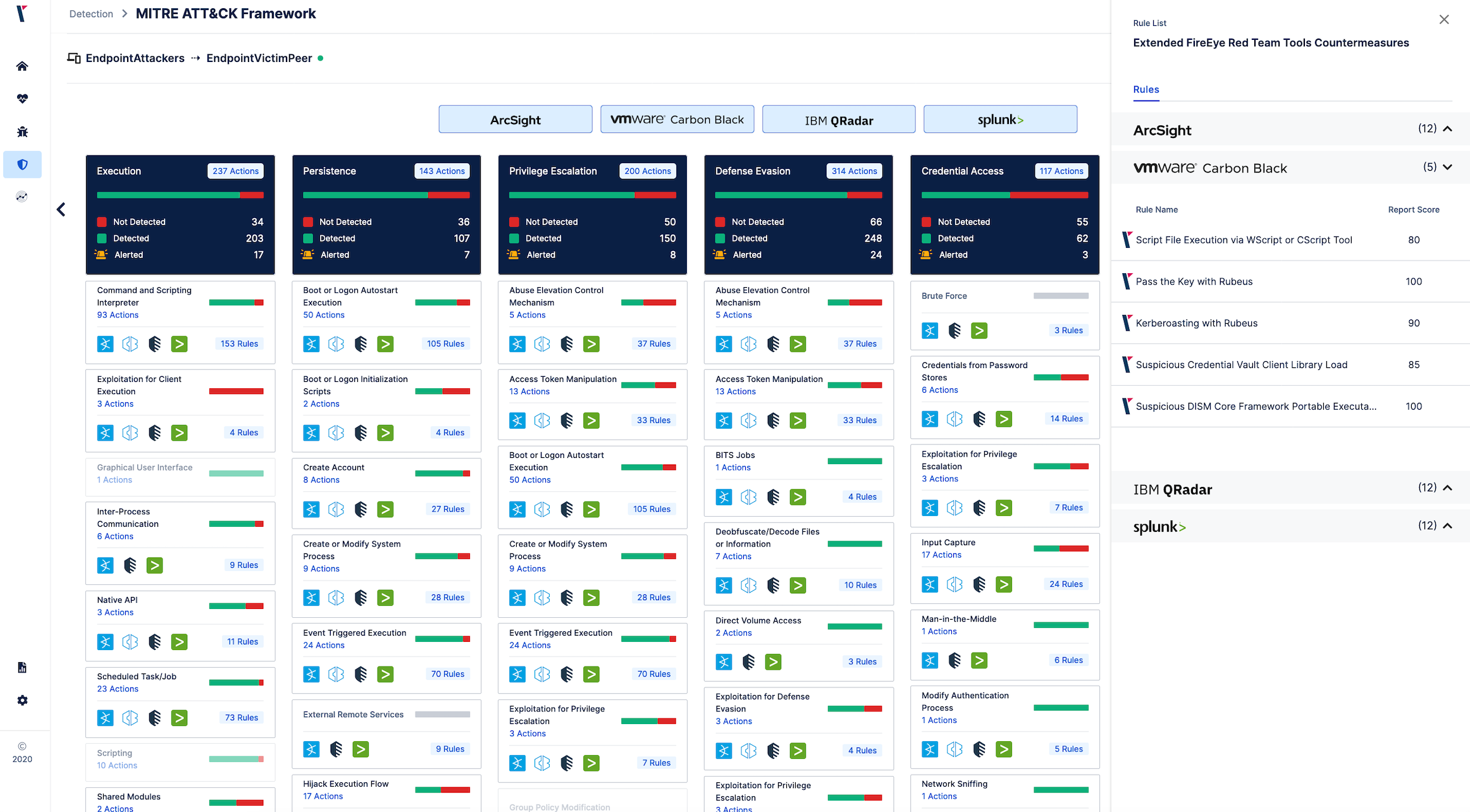
We analyzed tactics, techniques, and procedures utilized by threat actors of the FireEye’s stolen Red Team Tools. Attackers heavily used various defense evasion techniques.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
In 2013, Picus Security pioneered Breach and Attack Simulation (BAS) technology and has helped companies improve their cyber resilience since then. Established by cybersecurity veterans with academic backgrounds and extensive hands-on experience, Picus Security developed a transformative Security Validation solution for end-to-end attack readiness visibility and effortless mitigation to pre-empt cyber attacks across all cyber defense layers.
Tactics, Techniques and Procedures of FireEye Red Team Tools

Long Term Analysis Illustrates How Risk Posed by a Vulnerability

On FireEye Bashing-And-HotTakes (B&HT) and the ridiculous

The Stolen FireEye Red Team Tools Are Mostly Open Source
Red Teaming and MITRE ATT&CK Red Team Development and Operations

Red Team Assessment, Dubai
It is Time to Take Action - How to Defend Against FireEye's Red

Red Team tactics – breaching the lines of defense – Comsec Global
Electronics, Free Full-Text