Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
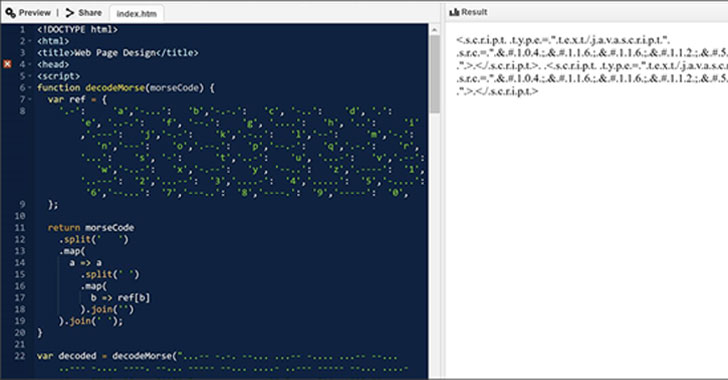
The Evolution of Malicious Shell Scripts
Rise in XorDdos: A deeper look at the stealthy DDoS malware targeting Linux devices
Don't believe these four myths about Linux security – Sophos News
The Evolution of Malicious Shell Scripts

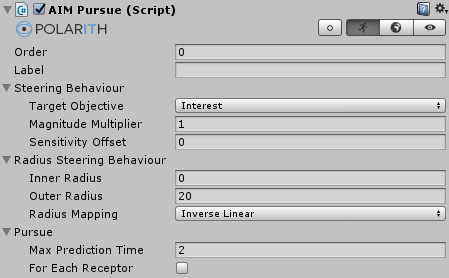
Windows Red Team Defense Evasion Techniques - HackerSploit Blog
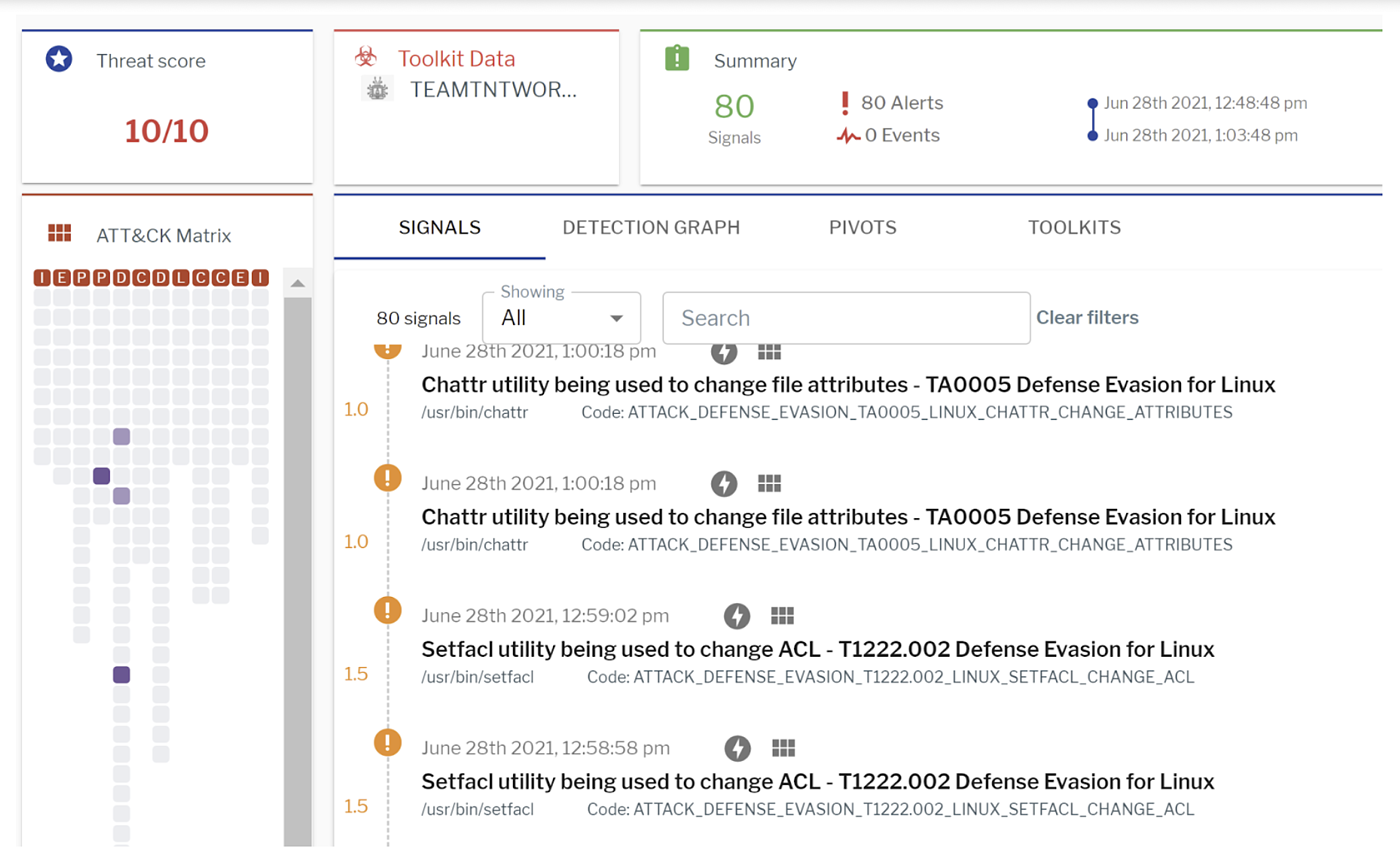
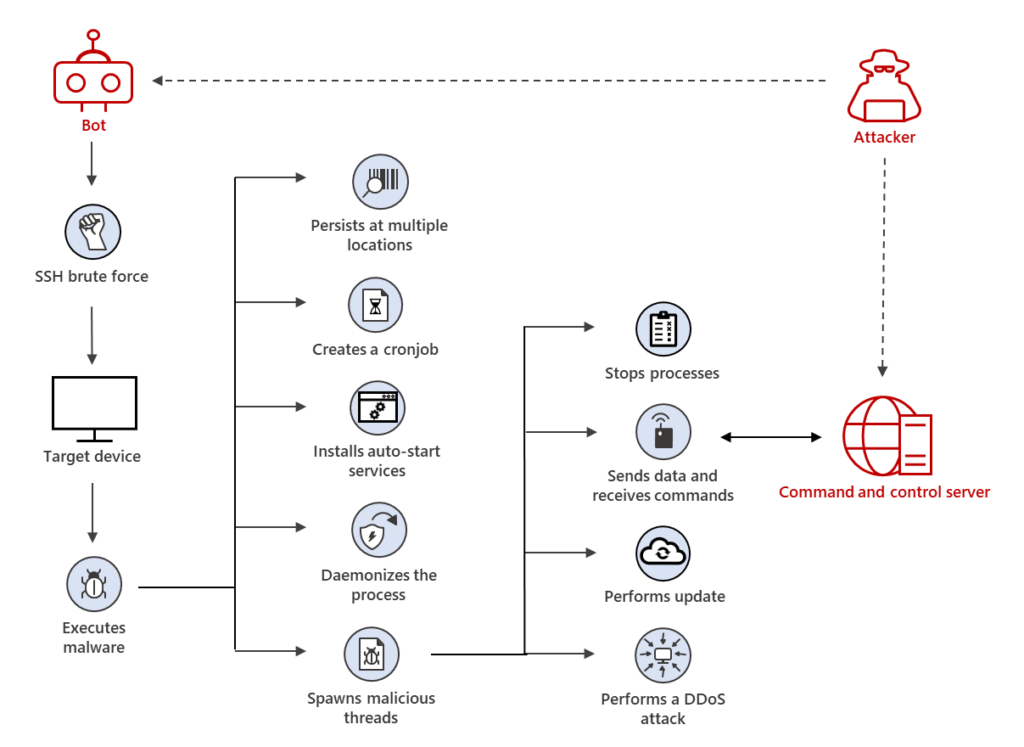
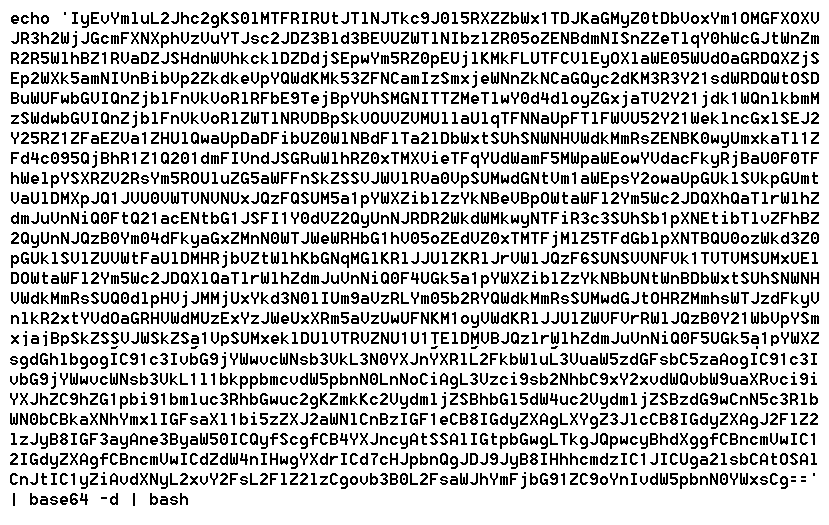
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
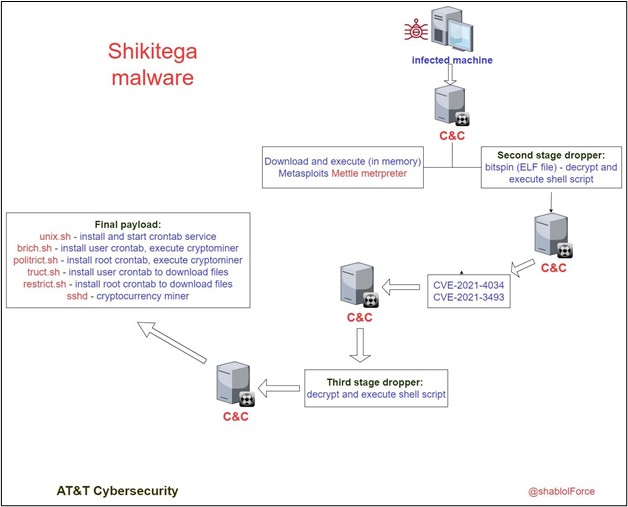
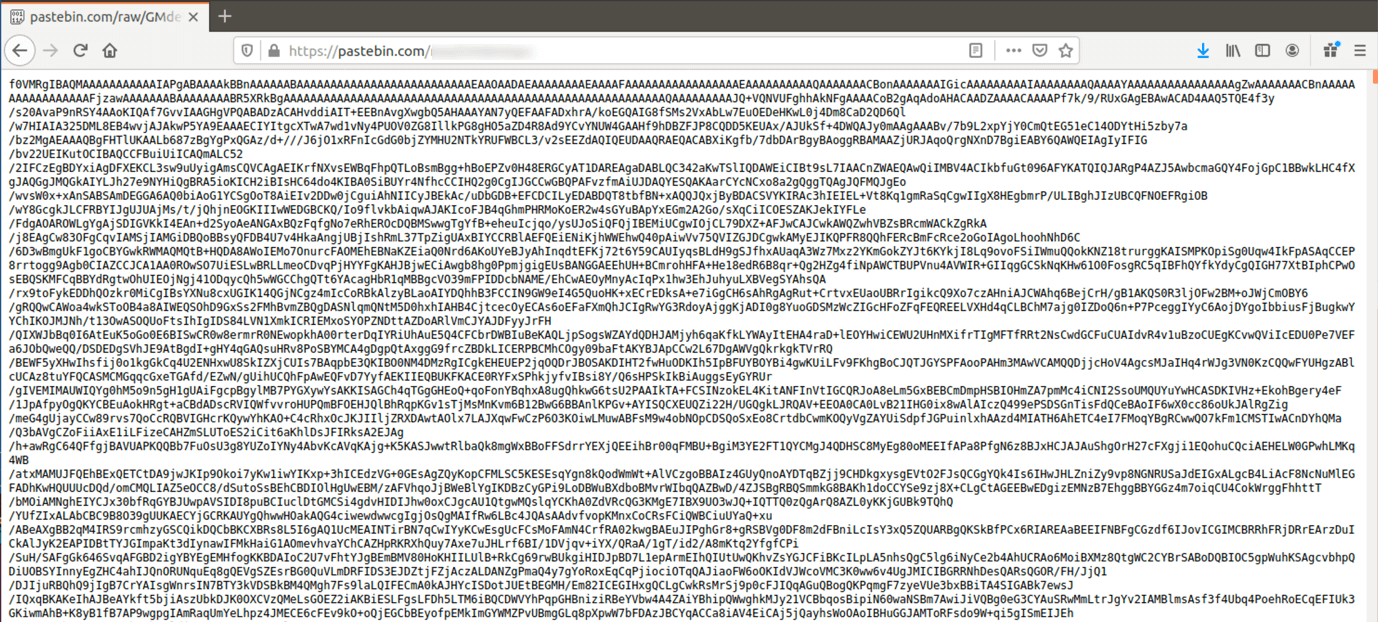
Shikitega - New stealthy malware targeting Linux
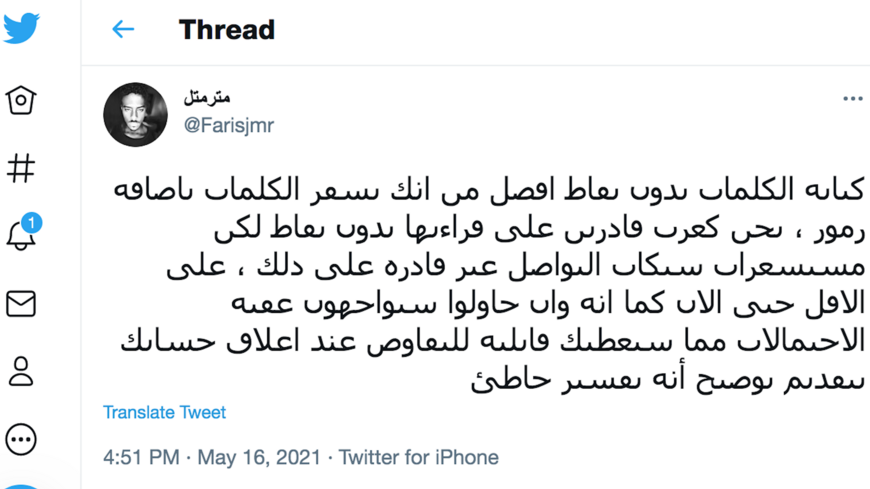
Examining the Activities of the Turla APT Group

Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
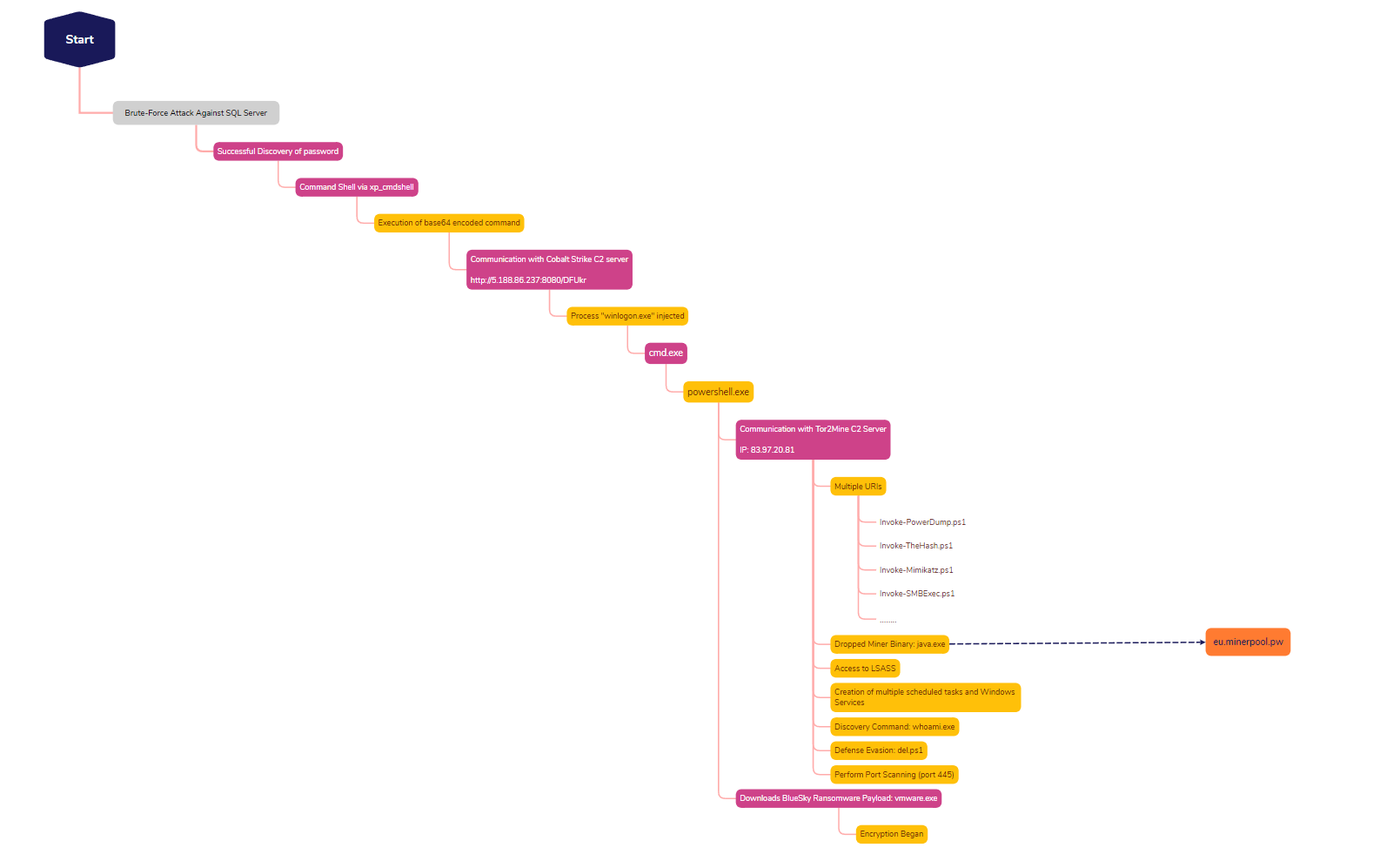
SQL Brute Force Leads to BlueSky Ransomware - The DFIR Report
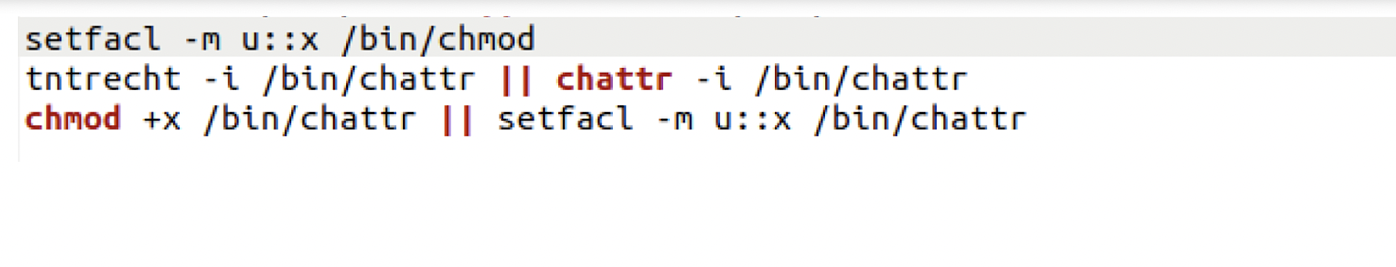
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them