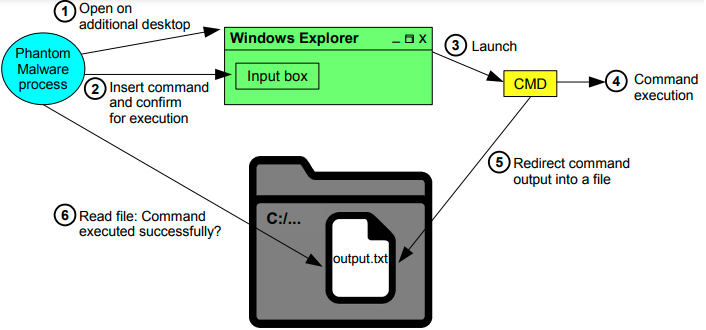
Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Malware Analysis: Protecting Your Network from Cyber Attacks

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
IEEE Access: The Multidisciplinary Open Access Journal

What to Include in a Malware Analysis Report

Krebs on Security – In-depth security news and investigation

How to build a malware analysis sandbox with Elastic Security

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights
GitHub - mesquidar/ForensicsTools: A list of free and open forensics analysis tools and other resources
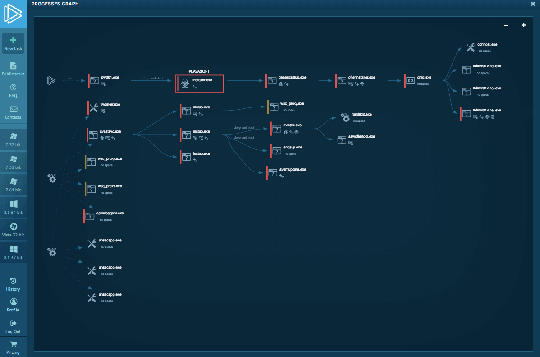
Interactive Online Malware Sandbox

Cybersecurity Search Engine

AlienVault - Open Threat Exchange

Malware analysis metasploit.bat Malicious activity

Endpoint Detection and Response, Free - What is EDR Security?
Most Common Malware Attacks