Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1 · Arch Cloud Labs

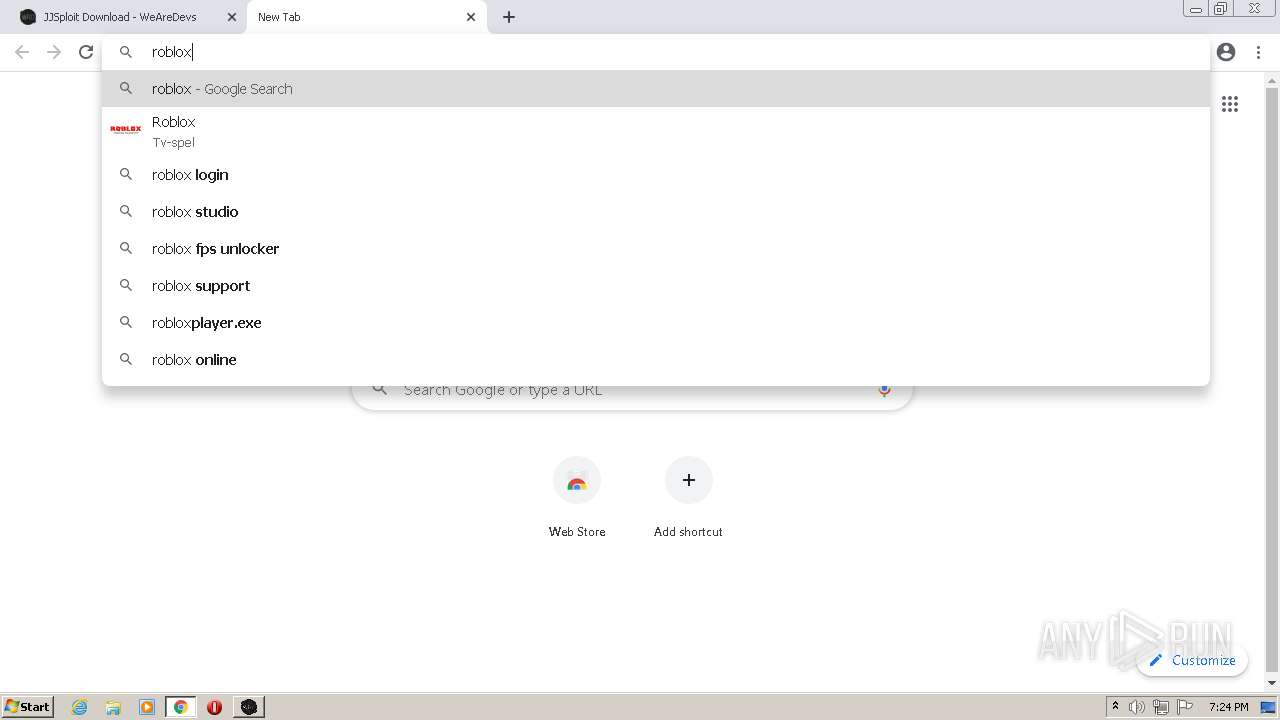
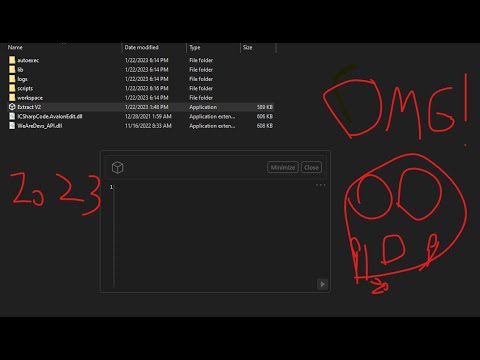
Malware analysis file Malicious activity
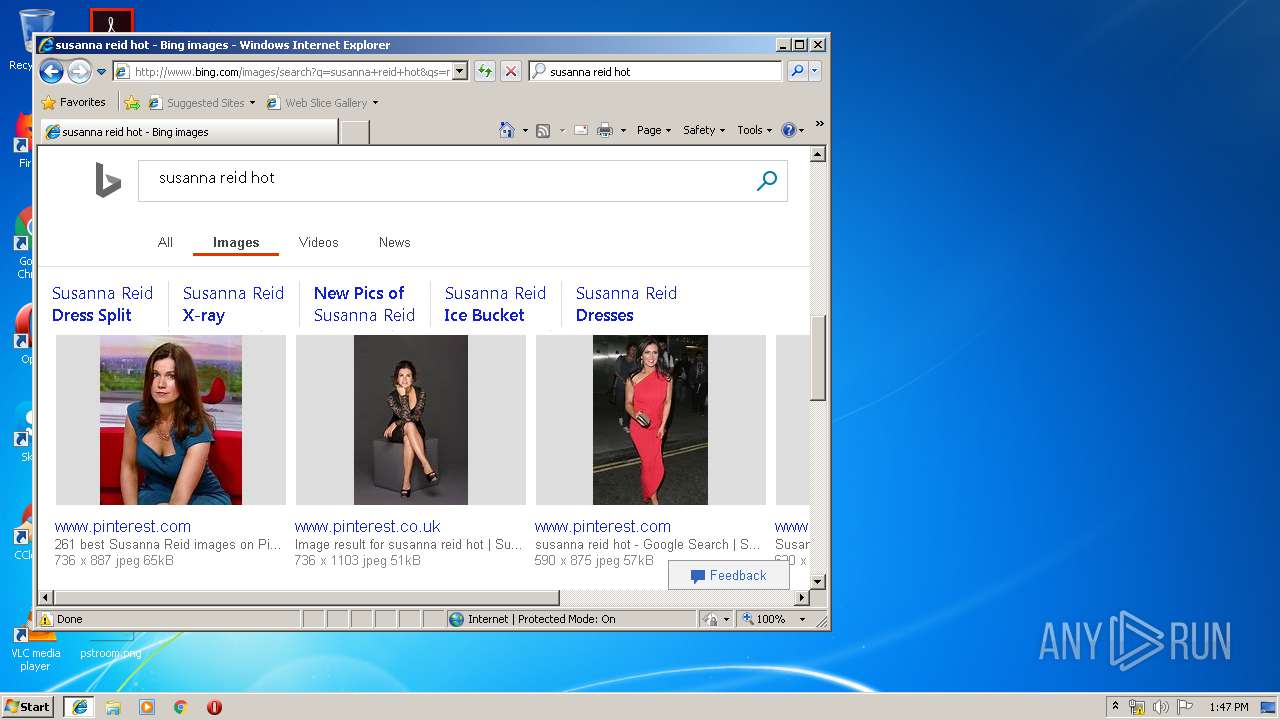
Malware analysis index.html Malicious activity

MetaDefender Cloud Advanced threat prevention and detection

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Dynamic malware analysis [34]
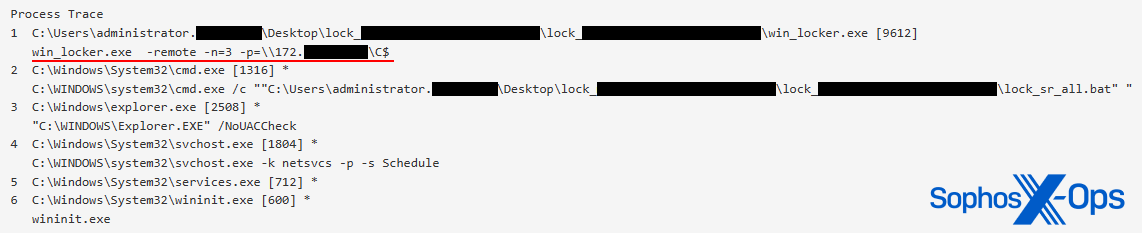
CryptoGuard: An asymmetric approach to the ransomware battle – Sophos News

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus
Malware analysis apksharp.com Malicious activity

Malware analysis mykey_.rar Malicious activity

Advanced Automated Malware Analysis – Kaspersky Research Sandbox
Most Common Malware Attacks

What to Include in a Malware Analysis Report